You Never Know
Jose's Blog
Sunday, 2 June 2024
Infinix GT 20 Pro - Budget Gaming Phone?
Tuesday, 28 May 2024
Samsung Galaxy F55 vs M55 vs A55: Battle of the Mid-Rangers
Performance
Display
Camera
Weight and Battery
Software
Sensors
- Accelerometer
- Fingerprint Sensor
- Gyro Sensor
- Geomagnetic Sensor
- Light Sensor
- Proximity Sensor(M55,F55)
- NFC
- Wifi-Direct
- Hall sensor(A55)
- Virtual proximity sensing(A55)
Tuesday, 26 December 2023
Living the Green Dream
Introduction: Meet George Kuzhivelil, a true inspiration for anyone seeking a sustainable lifestyle. For over a decade, he's been transforming his Kerala home into a green haven, proving that eco-friendly living is not just possible, but incredibly rewarding.
Solar Power Champion: In 2012, Dad's journey began with two solar panels. Fast forward to today, his rooftop boasts a 12-panel farm, silently capturing the sun's energy and lighting the way towards clean power.
Beyond Panels: Sustainability doesn't stop with electricity. Dad further reduced his environmental footprint by installing a solar water heater in 2016, ensuring a warm welcome while minimizing carbon emissions.Rainwater Harvest: Monsoon showers aren't wasted in Dad's home. Four strategically placed rainwater harvesting tanks collect the bounty, providing abundant water for plants, gardens, and even car washes throughout the year.
Waste to Energy: Embracing sustainable waste management, Dad installed a biogas fuel system. This ingenious system not only recycles waste but also generates clean cooking fuel, reducing reliance on traditional, often polluting sources.
Giving Back to the Grid: In 2021, Dad reached a remarkable milestone – becoming a net contributor to the KSEB electricity grid. His solar panels now produce more than his home consumes, making him not just self-sufficient but also an active contributor to the community's clean energy future.
A Visionary Path: Importantly, Dad embraced these sustainable practices long before they became trendy. He's a true pioneer, demonstrating that living green is not just about following the latest fads, but about a genuine commitment to the planet and a vision for a brighter future.
Conclusion: Dad's story is an inspiring testament to the power of individual action. His dedication to sustainability showcases the positive impact we can all have on our environment, one step at a time. So, let's take a page from Dad's green playbook and start our own journeys towards a more sustainable future!
Monday, 2 October 2023
CASE Connected vehicles
The car of the future is connected, autonomous, shared, electric – and it’s already here. For example, by 2030, more than 95 percent of passenger miles will be served by autonomous cars. With sensors now built into every imaginable aspect of a vehicle, from fully voice-operated features and driver attention monitoring to biometric security for reducing theft, the possibilities for the customer experience are endless. Car manufacturers have started thinking beyond traditional car features like design and engine type to consider cutting-edge digital capabilities like personalized subscription services where user can opt in or out of a range of on-demand features from a centralized marketplace.
Because of this, customers have changed the way they purchase cars – it’s not just about aesthetics or performance anymore. There is a shift in customer preferences to include features like personalized digital entertainment and data-powered productivity. Connected cars of the future will also offer facial recognition systems that change in-car settings for the driver, in-car gesture control and voice recognition for advanced security, and in-car shopping with geo-based prompts.
Research indicates that the automotive industry is a leading adopter of smart factories and use of digital technologies such as IoT connectivity, intelligent automation, and cloud-based data analysis and management. However, to take advantage and truly commercialize on the possibilities of the connected vehicle, automotive leaders need to ensure they have a strong technological foundation and that they are:
- Adopting next-gen capabilities that will drive innovation. This includes 5G, cloud, and AI. In fact, up to 15 percent of all new vehicles sold in 2030 could be fully autonomous using next-gen capabilities.
- Conforming to safety and security demands. Given the sensors and the data-driven nature of connected vehicles, they may be more prone to hacking. But turning control completely over to software could lead to new hacking vulnerabilities and other liability issues that companies cannot ignore. To overcome this, automotive companies have to allow drivers to intervene in emergencies.
- Choosing the right operating systems, hypervisor options, embedded software design, and hardware compatibility. These parameters are critical factors to consider given the increasing share of electrified vehicles as a percentage of new vehicle sales. For electrified vehicles, it’s important to have the right OS and embedded software and software.
- Enabling rapid prototyping, development, and testing/verification. There’s no denying that the future of the automotive industryis tied closely to additive manufacturing. Continued innovations in the 3D printing industry – including new materials, printers, and techniques – will continue to change the way companies design and create. To remain competitive, or simply stay relevant, organizations need to adopt smarter and faster ways to prototype and develop.
- Enhancing the capabilities behind design and production. A connected vehicle requires multiple end-to-end capabilities. The industry is in a critical period of disruption, and those who build in the software capabilities in the same way they think about hardware will be able to win mindshare and market share over the long term.
- Think beyond the vehicle. For connected cars, the ecosystem is not just within the vehicle. Because of this, automotive manufacturers need to work with fleet suppliers and service providers to deliver sustainable, connected value across the ecosystem. For example, automobile manufacturers need to work with city planners for better sustainability options such as placement of electric vehicle charging stations based on data.
Monday, 21 August 2023
What's the value of an Industry Cloud
Here is a short video https://www.youtube.com/watch?v=lXJyYOHXjqw in which I explain this Capgemini #technovision2023 trend and read the full report on https://www.capgemini.com/insights/research-library/technovision-2023/
Tuesday, 18 July 2023
Java String Program - Part 1
Program 1
Program 2
Program 3
Video explanations for these programs
Saturday, 15 July 2023
Java - Bubble Sort Numbers and Strings
Bubble sort code for sorting numbers in ascending order
public class Bubble_Asc{
public static void sort_number_asc(){
// input array elements
Scanner sc = new Scanner(System.in);
int a[] = new int[5];
System.out.println("Enter five array elements");
for(int i=0; i<a.length; i++){
a[i] = sc.nextInt();
}
// sort array elements
for(int i=0; i<a.length; i++){
for(int j=0; j<a.length-1-i; j++){
if( a[j]>a[j+1] ){
//swap elements
int temp = a[j];
a[j] = a[j+1];
a[j+1] = temp;
}
}
}
// output the sorted array
System.out.println("Sorted array is");
for(int i=0; i<a.length; i++){
System.out.print(a[i] + " ");
}
}
}
Bubble sort code for sorting numbers in descending order
Bubble sort code for sorting strings in ascending order
Bubble sort code for sorting strings in descending order
Monday, 10 July 2023
Java - Class based program
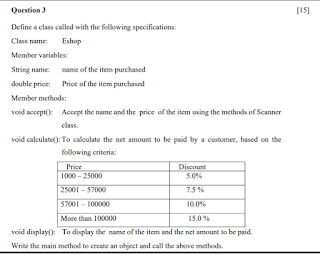
Program 1 - Eshop
Program 2 - CabService
Program 3 - employee
class employee{
// member variables
int eno;
String ename;
int age;
double basic;
double net;
// member methods
void accept(){
Scanner sc = new Scanner(System.in);
System.out.println("Enter eno, ename, age, basic salary");
eno = sc.nextInt();
ename = sc.next();
age = sc.nextInt();
basic = sc.nextDouble();
}
void calculate(){
double hra = 18.5/100.0 * basic;
double da = 17.45/100.0 * basic;
double pf = 8.10/100.0 * basic;
net = basic + hra + da - pf;
// net = basic + (18.5/100.0*basic) + (17.45/100.0 * basic) - (8.10/100.0 * basic);
if (age > 50)
{
net = net + 5000;
}
}
void print(){
System.out.println("eno \t ename \t age \t basic \t net");
System.out.println(eno + "\t" + ename + "\t" + age +
"\t" + basic + "\t" + net );
}
public static void main(){
employee obj = new employee();
obj.accept();
obj.calculate();
obj.print();
}
}
Explanation of above code can be found at
Infinix GT 20 Pro - Budget Gaming Phone?
Gamers, strap yourselves in! Calling all mobile warriors and esports enthusiasts, the Infinix GT 20 Pro has just entered the arena. This r...

-
In the earlier parts of this article I described some technical tuning tips specific to a slow-performing Weblogic JEE server. Another earli...
-
When running Maven, if you try to run multiple Maven commands in a batch (.bat) file, it only runs the first one and exits to the ...